
In this age of the Internet of Things (IoT), the security of embedded systems is vital for any organisation’s computer systems. Security for embedded systems is a methodology whereby organisations create the correct level of protection for the data contained within and transmitted or received by any embedded device. This methodology of security in embedded systems must cover the entire life cycle of the device or system.
Embedded systems are devices with a dedicated function that are part of a more extensive system. For example, the security alarms, air conditioning, refrigerator, and furnace controls could all be embedded systems within a smart house.
Other embedded systems within the business world could be control and instrumentation switches, pumps, computer network switches and routers, blood pressure monitors and oxygen supplies in hospitals, beacons in air traffic control, management systems in aircraft, and collision avoidance systems in cars. Every modern system has many of these small devices doing a specific job, and increasingly they are being viewed as a doorway into the larger system by cyber criminals.
The embedded security market is rapidly growing due to the increasing number of connected devices, including the Internet of Things (IoT device security) and the Industrial Internet of Things (IIoT). Embedded devices require specific security to prevent unauthorized access, protect sensitive data, and ensure system integrity.
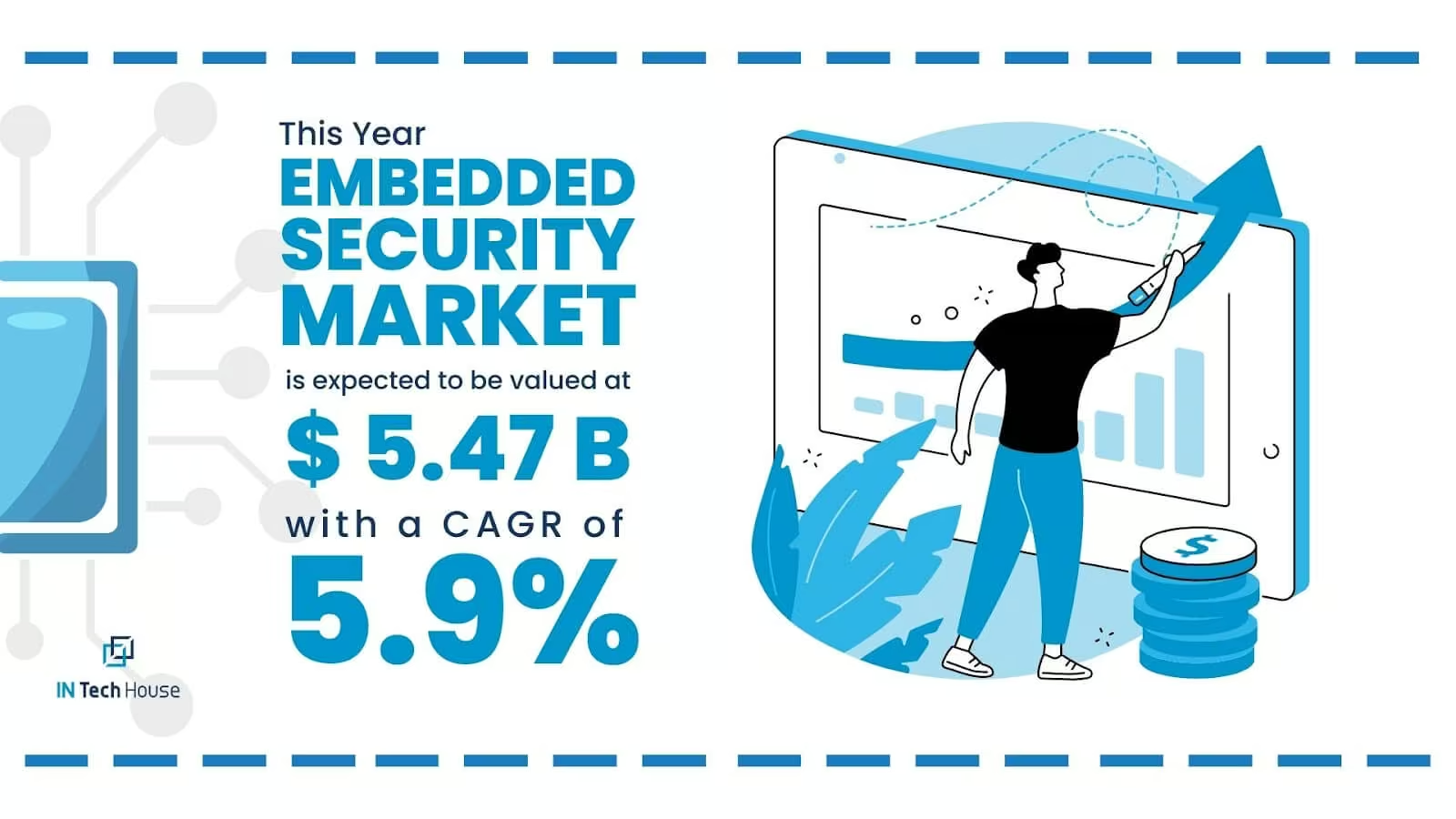
Source: PRNewswire
The market is expected to grow significantly in the coming years due to increasing demand from various industries such as automotive, healthcare, aerospace, and defence. The market is also being driven by the growing demand for security solutions in the banking and financial sector.
Some of the key trends in the embedded security market include the increasing use of artificial intelligence (AI) and machine learning (ML) to detect and prevent security threats, the integration of hardware-based security solutions, and the adoption of blockchain technology for enhanced security.
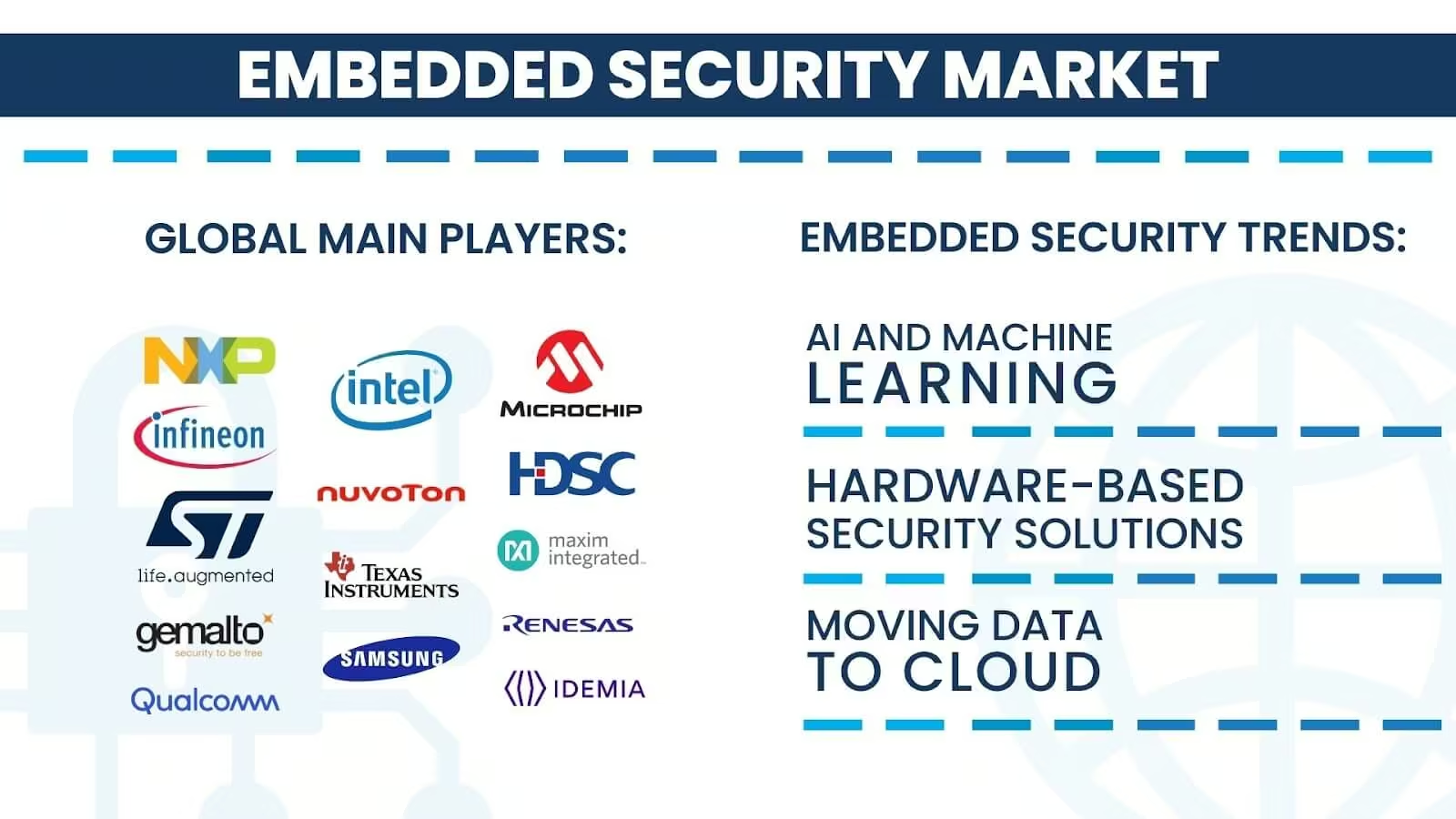
Source: MordorIntelligence, The ExpressWire, INTechHouse Projects
The market is also being driven by the increasing demand for cloud-based security solutions, as more organizations are moving their data to the cloud. This is leading to the adoption of advanced security solutions such as secure boot, secure firmware updates, and secure communications.
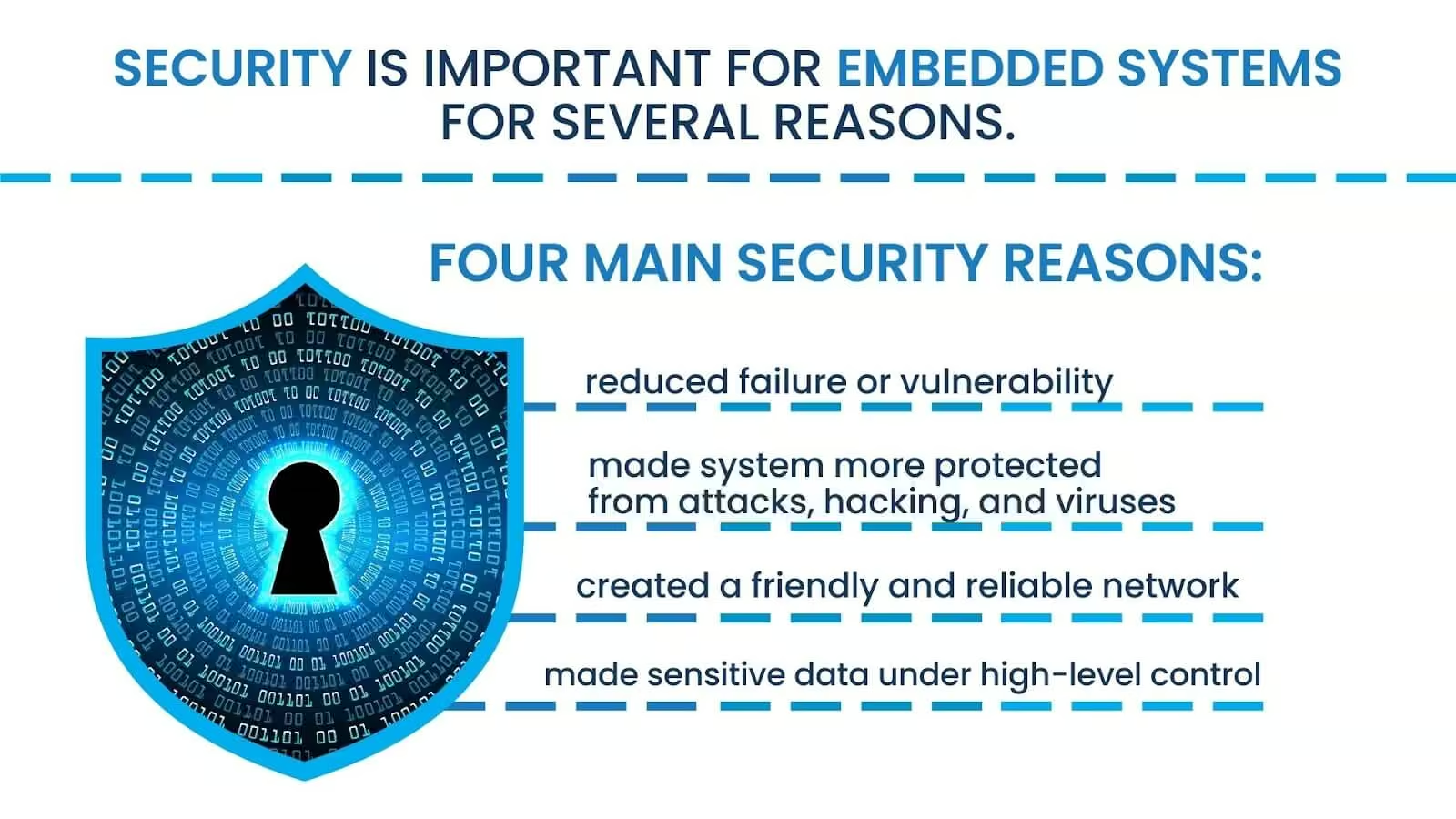
Firstly, embedded systems are often used in critical applications such as healthcare, automotive, and aerospace, where any failure or vulnerability can have serious consequences.
Secondly, embedded systems often have limited resources and may not have the same level of security features as other systems. This makes them vulnerable to attacks such as malware, viruses, and hacking.
Thirdly, embedded systems are often connected to other systems or networks, making them potential entry points for attackers to gain access to sensitive data or systems. Therefore, it is essential to ensure that security measures are implemented in embedded systems to protect against these threats.
Protecting embedded systems begins with the design of any device. Not only must the design team ensure that the device performs its intended job, but they must also consider embedded systems vulnerabilities. It’s no longer sufficient to only look at the embedded hardware security. Design teams must also address issues such as unauthorised access and the modification or destruction of the device. Embedded software security is a vital component of this entire process, and managing and updating this security over the device’s lifecycle is essential as threats constantly evolve.
As we’ve said, securing embedded systems security involves securing the device’s hardware and software. Let’s examine some aspects of how to secure embedded systems.
Physical SecurityThe first step in these processes is to manage the embedded device security. Some hardware vulnerability examples are environmental requirements such as heat, cold, waterproofing, chemical proofing, shock proofing, and hardness. Keypads are inherently vulnerable and must be secured, but the internal components must also be secured. Radiation protection, immutable memory, and eFuses could all be part of this protection, depending on where the embedded device will be used.
Embedded software security revolves around managing and responding to malicious attacks at start-ups or during regular running. This includes device authentication, authentication on a network, firewalls and other protection between the device and the network, and hardening of the device software to prevent unauthorised manipulation, especially during any upgrades.
It’s almost impossible to place a monetary value on the data owned by an organisation, making cyber security for embedded systems imperative in our wired world. Modern embedded devices are mission-critical components in many systems, making them popular targets for hackers and cybercriminals. These devices can present a significant security loophole without embedded cyber security.
Cyberattacks on embedded devices range from overcoming anti-theft devices in motor vehicles to downgrading the performance of control systems for electricity grids, petroleum pipelines, defence systems, and other significant manufacturing and infrastructure systems. Confidential commercial information has been stolen by a hacker directing confidential reports to their own printer or delving into a corporate cell phone.
Many businesses simply do not know that they have been attacked and live in a world of illusions that they have good security. As the experience of many companies shows, if you do not think about cyber security, you can become a blind kitten from the network and not be prepared for dangers at all.If you do not deal with security, in most cases it will result sideways for business…maybe not now, but in a couple of years, but it will pour out. And here we will talk not only about losses, but about reputation, values and, it seemed to be, simple savings or inattention to the business process and many years on the market can come to nought. Why take such a risk?
Global brands can emphasize the importance of embedded cyber security in ensuring the safety and reliability of their products. They can highlight the steps they take to ensure that their embedded systems are secure, such as regular security assessments and updates, certain coding practices, and the use of encryption and authentication protocols.
They can also share success stories of how their embedded cyber security measures have prevented cyber attacks and protected their customers’ data and privacy. Doing so can build trust with their customers and stakeholders and demonstrate their commitment to cyber security.
Securing embedded systems involves implementing several methods and techniques to prevent attacks and ensure the safety of the system. Here are some of the most commonly used methods and techniques:
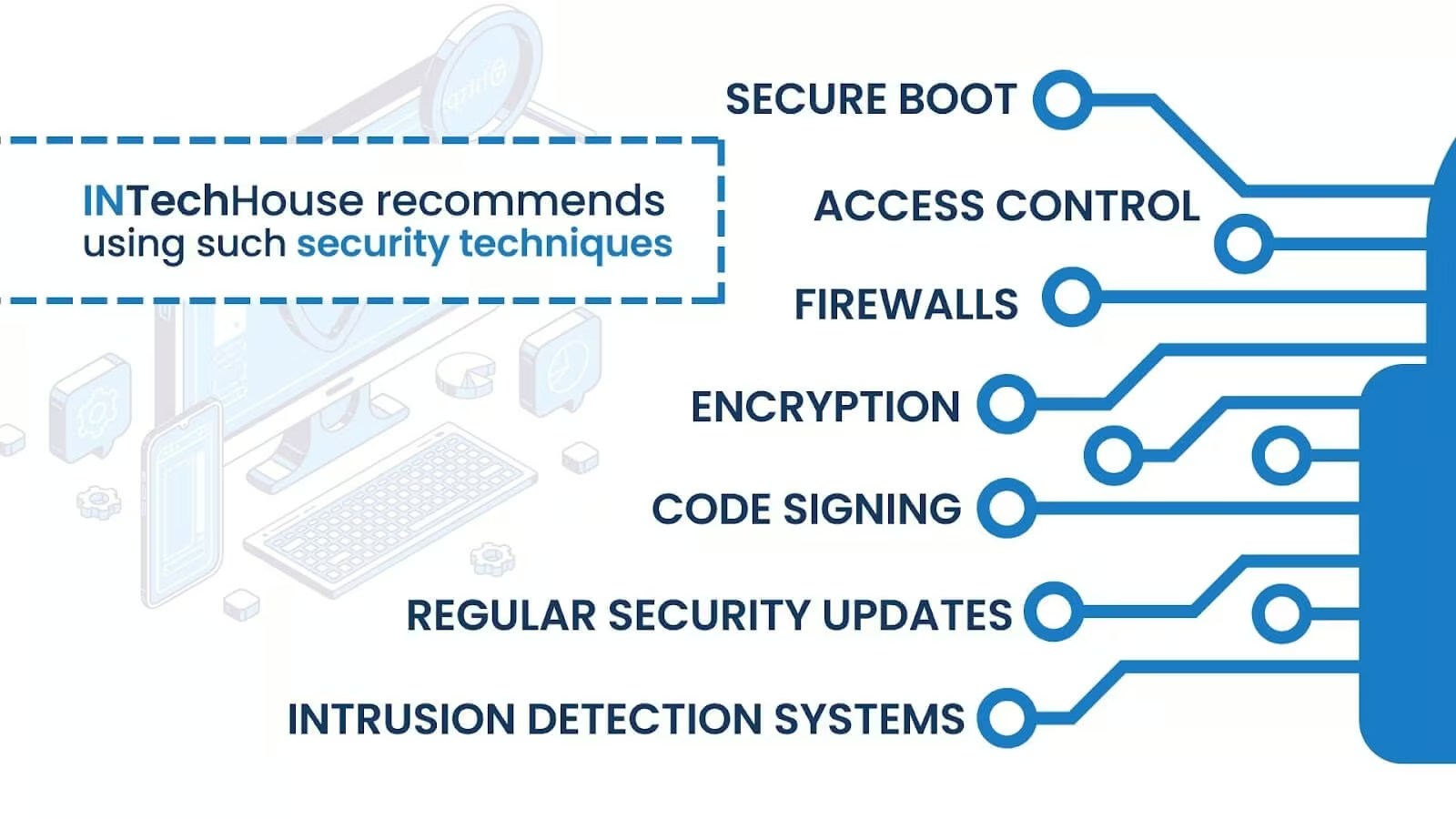
Implementing these methods and techniques can help to ensure the security of embedded systems. However, it’s essential to have a comprehensive security strategy and regularly assess the system’s security to stay protected against emerging threats.
The security in embedded systems design challenges faced by designers can be monumental. The first challenge is the lifecycle of the device. Many devices are installed in systems intended to remain in play for decades. Consider motor vehicles, power plants, and other mission-critical systems with 20 years or longer lifespans. The vulnerabilities and challenges that the device will face are impossible for the designers to predict at the start of the device’s lifespan.
This means the device must be updatable, and the components must be replaceable. As devices age, they cannot process the latest in software, so chips must be able to be replaced. If the device is installed in a hostile environment, it must be replaced by a robot, further complicating the design process.
Updating the software in a fridge, smart TV, or cellphone is easy and has little impact on the user. Updating the software in a mission-critical system or a system protecting life, such as medical systems, has to be managed extremely carefully, as the impact can be deadly.
Cyber security embedded systems are vital for any device that is to be installed in any piece of equipment that is to be connected to the internet. The only safe system is turned off; the next is a system isolated from the internet. Unfortunately, neither of these options is available, so designers of these devices must take embedded security seriously.
Physical security is a starting point, but the software must be protected, as must the network, to prevent cyber attacks. Security must be built from when a hand holds a pencil to outline until the device is finally scrapped as it’s declared obsolete and replaced.

He leads complex engineering programs at Intechhouse, an EU-certified R&D Center, delivering advanced solutions across aerospace, defense, oil & gas, and telecommunications. His work focuses on solving high-impact technical challenges and driving innovation in demanding, mission-critical environments.With deep expertise in designing reliable, scalable electronic systems and a strong track record of leading cross-disciplinary teams, he specializes in hardware integration and embedded technologies. Krzysztof also shares his knowledge as a contributor and mentor, focusing on electronics design, system architecture, and engineering best practices.
This initial conversation is focused on understanding your product, technical challenges, and constraints.
No sales pitch - just a practical discussion with experienced engineers.
Share a few details about your product and context. We’ll review the information and suggest the most appropriate next step.