
In the rapidly evolving digital landscape, data integrity forms the bedrock of reliable information systems. For organizations like INTechHouse, which rely on accurate data for strategic decisions, understanding and maintaining data integrity is not just necessary - it's vital.
At its core, data integrity is about ensuring the accuracy, consistency, and reliability of data throughout its lifecycle. It involves a combination of practices, technologies, and policies designed to keep data pure and unadulterated from its creation to its deletion.
While closely linked, data integrity differs from data security. Data security focuses on safeguarding data from unauthorized access and breaches. However, integrity encompasses the correctness and consistency of data, independent of its security status.
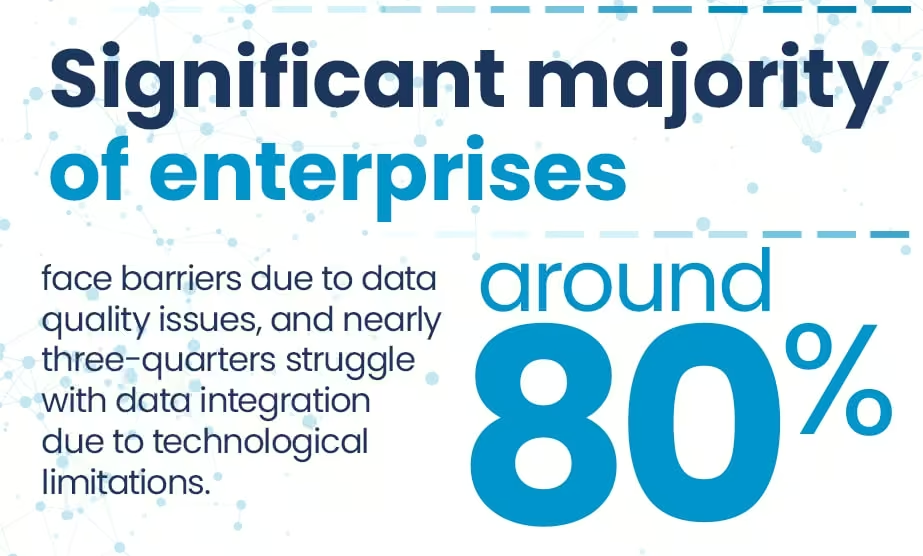
Source: Precisely
Data integrity challenges can stem from multiple sources, often leading to far-reaching consequences for business insights and operations.

When data integrity is breached, the repercussions can be significant. Decisions based on flawed data can mislead business strategies, resulting in operational inefficiencies and financial losses. Therefore, INTechHouse must employ robust measures to ensure the integrity of their data.
Implementing a comprehensive approach that combines technology solutions, stringent policies, and regular audits can help maintain high data integrity standards. Employee training and awareness are also critical in reducing human error. Additionally, employing advanced data management and protection tools can safeguard against software and hardware failures.
Data Validation:
Data validation is the process of ensuring that data is accurate, consistent, and reliable. This involves implementing checks and validations to detect errors, inconsistencies, or anomalies in the data before it is stored or processed.
Error Checking:
Error checking involves identifying and correcting errors that may occur during data entry, transmission, or processing. This includes implementing error detection mechanisms, such as checksums or parity bits, to verify data accuracy and integrity.
Audit Trails:
Audit trails provide a comprehensive record of data access, changes, and transactions, allowing organizations to track and monitor data usage, detect unauthorized activities, and maintain accountability.
Data Governance Framework:
A comprehensive data governance framework establishes policies, processes, and controls to ensure that data is managed, protected, and utilized effectively throughout its lifecycle. This framework defines roles and responsibilities, establishes data quality standards, and promotes transparency and accountability in data management practices.
Database Management Systems (DBMS):
DBMS platforms offer built-in features and functionalities to support data integrity, such as data validation rules, constraints, and transaction management capabilities. These systems ensure data consistency, reliability, and durability, helping organizations maintain data integrity across their databases.
Data Validation Tools:
Data validation tools automate the process of validating and verifying data against predefined rules, patterns, or criteria. These tools identify data errors, inconsistencies, or outliers, enabling organizations to proactively address data quality issues and maintain data integrity.
Backup Solutions:
Backup solutions create copies of data and store them in secure, offsite locations, protecting against data loss due to hardware failures, disasters, or cyberattacks. By implementing regular backups and data recovery processes, organizations can ensure data availability and integrity in the event of unforeseen incidents.
Blockchain Technology:
Blockchain technology provides a decentralized, immutable ledger for recording transactions and data entries. By storing data in a distributed network of nodes and cryptographically securing each transaction, blockchain ensures data integrity and tamper resistance, making it ideal for applications requiring verifiable and auditable records.
Dealing with Large Data Volumes:
Integrating Data from Diverse Sources:
Real-time Data Integrity Monitoring and Remediation:
Examining real-world case studies provides invaluable insights into successful data integrity implementations and offers lessons learned for organizations aiming to fortify their data assets. Let's delve into examples of organizations that have effectively implemented strategies to ensure data integrity.
As organizations deal with increasingly complex datasets and face evolving cybersecurity threats, the role of artificial intelligence (AI) and machine learning (ML) in ensuring data integrity has become more prominent. AI and ML algorithms can analyze vast amounts of data to detect patterns, anomalies, and potential security breaches in real-time.
With the proliferation of data privacy regulations and increased scrutiny on ethical data practices, regulatory compliance has become a driving force behind data integrity initiatives. Organizations must not only ensure the accuracy and reliability of their data but also adhere to stringent regulatory requirements and ethical standards.
Data integrity is crucial for maintaining the accuracy, consistency, and reliability of data throughout its lifecycle. It ensures that data is complete, accurate, and trustworthy, enabling organizations to make informed decisions, maintain regulatory compliance, and build trust with stakeholders. Without data integrity, organizations risk making flawed decisions, experiencing compliance violations, and damaging their reputation.
To ensure data integrity compliance, organizations can implement several key practices:
Data integrity risks encompass various threats and vulnerabilities that can compromise the accuracy, consistency, and reliability of data. Some common data integrity risks include:
While data integrity and data security address distinct aspects of data protection, they are closely interconnected and mutually reinforcing. Ensuring data integrity is foundational to maintaining data security, as accurate and reliable data is essential for effective security measures. Conversely, robust data security measures help safeguard data integrity by preventing unauthorized access, tampering, or corruption.
Data may work. It's not a nice slogan.Safeguarding data integrity is not just a necessity but a strategic imperative for organizations operating in today's data-driven world. By adhering to key principles, leveraging advanced technologies, and staying abreast of emerging trends, organizations can fortify their data assets, maintain trust with stakeholders, and drive innovation and growth. From implementing robust data governance frameworks to embracing AI and machine learning for anomaly detection, the journey to data integrity excellence requires diligence, adaptability, and a commitment to ethical data management practices.
At INTechHouse, we understand the critical importance of data integrity and are dedicated to partnering with organizations to navigate the complexities of data management and safeguard their data assets. Whether it's implementing cutting-edge technologies, designing comprehensive data security solutions, or providing expert guidance on regulatory compliance and ethical data practices, we're here to support your journey to data integrity excellence. Contact us today to learn more about our data management solutions and how we can help you achieve your data integrity goals.
There are several types of data integrity, including domain integrity, physical integrity, entity integrity, logical integrity, referential integrity, and user-defined integrity. Each type focuses on different aspects of ensuring the accuracy, consistency, and reliability of data.
Domain integrity refers to the validity and consistency of data values within a specific domain or set of values. It ensures that data entries conform to predefined rules or constraints, such as data type, range, or format, to maintain data accuracy and reliability.
Physical integrity pertains to the physical storage and transmission of data, ensuring that data remains intact and unaltered during storage, transfer, or processing. It involves measures to protect against data corruption, loss, or unauthorized modifications.
Entity integrity ensures that each record or entity in a database table is unique and has a primary key that uniquely identifies it. It prevents duplicate or null values in primary key columns, maintaining data consistency and relational integrity.
Logical integrity refers to the consistency and accuracy of relationships and dependencies between data elements or entities within a database. It ensures that data relationships and constraints are maintained, preserving the logical structure and integrity of the database.
Referential integrity enforces consistency and integrity between related data in different tables within a database. It ensures that foreign key values in one table correspond to primary key values in another table, maintaining data relationships and preventing orphaned records.
User-defined integrity involves custom rules, constraints, or business logic defined by users to enforce specific data integrity requirements beyond standard database constraints. It allows organizations to tailor data integrity measures to their unique business needs and requirements.
While data integrity and data security are closely related concepts, they are not the same. Data integrity focuses on ensuring the accuracy, consistency, and reliability of data, while data security is concerned with protecting data from unauthorized access, disclosure, or tampering. While both are critical aspects of effective data management, they address different dimensions of data management and require distinct strategies and measures to address effectively.

An expert in Artificial Intelligence, professor and researcher, who has authored numerous scientific publications and led international projects focused on AI, machine learning, and data-driven systems.
His work connects academic research with industrial applications, applying advanced AI models to practical challenges across sectors such as defense, telecommunications, smart industry, and cybersecurity. He has extensive experience in designing and implementing intelligent systems in complex, high-demand environments.
In addition to his technical work, Prof. Andrysiak shares insights on AI trends and applications as a speaker, mentor, and author, contributing to discussions on the role of AI in modern technology and digital transformation.
This initial conversation is focused on understanding your product, technical challenges, and constraints.
No sales pitch - just a practical discussion with experienced engineers.
Share a few details about your product and context. We’ll review the information and suggest the most appropriate next step.